This is the fourth part (of 5 ) of a paragraph by paragraph commentary on a recent article posing as journalism in the March 6, 2017 issue of The New Yorker. I hope to demonstrate that this article is basically a totally mendacious concoction of cold war US propaganda constructed out of unsubstantiated opinions expressed by US government officials and various journalists and others who are hostile to the current Russian government. There are a few paragraphs exempt from this characterization and they are duly noted. I have put a link to the article itself so that my commentary can be compared, paragraph by paragraph, to the original. However, the commentary can be read on its own. I contend it expresses the real meaning of the original paragraph and my evaluation of that meaning. The original is there for anyone to check to see if I have distorted rather than clarified what the paragraph’s actual meaning is. It is my position that this article is junk journalism which misrepresents the objective reality it purports to describe and that my commentary points out the misrepresentations and attempts to correct them. I hold that no self respecting journalist would write an article such as this New Yorker piece and palm it off on the public. My commentary is also an object lesson on how to distinguish between reportage that at least attempts to be unbiased and obvious nonobjective propaganda. You will know more about Trump, Putin and the New Cold War from the commentary than you will ever know from the original article.
Trump, Putin, and the New Cold War – The New Yorker
Active measures were used by both sides throughout the Cold War. In the nineteen-sixties, … Evan Osnos joined The New Yorker as a staff writer in 2008, …
www.newyorker.com.iconewyorker.com/magazine/2017/03/06/trump-putin-and-the-
Section Four: “Hybrid War” 37 Paragraphs
1. Russia wasn’t very advanced in computer technology. It didn’t get on the world wide web until 1990. However, it caught up and by 1996 it had expert hackers and now “cyber tactics have become an essential component of Russia’s efforts to exert influence over its neighbors.” [The US of course does exactly the same: no great revelation here].
2. Spring 2007, somebody cyber attacks Estonia: news, banks and government sites go down.
3. Russia and Estonia were at odds over Estonia’s decision to move a Soviet WWII war memorial (a statue of a soldier) out of the capital’s (Tallinn) center.
4. April 27, 2007 the statue is removed. Soon Estonia’s sites were flooded with DDoS (Distributed Denial of Service) disabling them for two weeks. [Who did it? Angry Russians living in Estonia? The Russian government? Private Russian computer trolls? Political enemies of the current Estonian president?] “Investgators never pinpointed” who did it. In other words, nobody knows who did it so let’s blame the Russian government. [This is very analogous to the current blame laid at the feet of Putin for the “hacking” of the DNC and the US elections. The Russians could have done it therefore the Russians did it.] The then Estonian President (Toomas Ilves), who left office last year, is not content to just blame the Russians but believes it was the Russian government + “mafiosos”: and why not? Without evidence you can cast blame wherever you feel like.
5. What do the authors of the New Yorker article conclude? Well, they don’t know exactly what happened but they do know what the ex-president thinks happened, or rather believes happened, therefore “it was a landmark event: a state-backed cyber-attack for political purposes.” And to reinforce their conclusion they quote a Pentagon official who doesn’t know anymore about who did it than they do. A shining example of first rate investigative journalism.
6. 2008 Russian tanks crossed over into South Ossetia in the former Soviet Georgia [they don’t mention until later that the Georgians open fire first ] and at the same time hackers disabled the Georgian internet. In “defense” circles the Russians were becoming well known for their “ambition, technical acumen, and speed.’’
7. The Georgia operation showed that the Russians knew how to coordinate cyber activity and ground operations [could walk and chew gum at the same time].
8. The Russians were, however, upset over the propaganda side of the Georgia operation. Although they released the films proving the Georgians attacked first when these films were presented in the Western media they were made to look as if the Russians attacked the Georgians. The authors remark that “Russian generals took this lesson to heart.” As a result they made a study of “information war” and how to use the media more effectively, putting what they learned to use in Ukraine and Syria. I wonder if the authors are aware of the meaning of their own paragraph? The Russians give the proof of who started the fighting in Georgia to the Western “free press” and media and the information is altered to conform to a US disinformation campaign at the time which alleged that the Russians started the fighting. One of the points the authors are trying to make in their article is the Russian press is obedient to Putin while the Western press tells the truth. It reminds me of the German news reels in 1939 that showed Poland invading Germany and starting the war. The author’s own words imply the Russians just recently learned “disinformation” from the Western press. [What? All those years under Communism “Pravda” was telling the truth!]
9. The authors report that the US was also successful in waging a cyber attack around this time. In 2008 the US and Israel teamed up and placed a “worm” into an Iranian network to make their “centrifuges to spin out of control” to slow done Iran’s “nuclear development.” [The US is proud of this achievement yet voices in Congress say it’s a casus belli if the Russians spied on the DNC and told WikiLeaks what they found out.]
10. A meaningless paragraph about our so-called “reset policy” with Russia and a quote from the hawkish Evelyn Farkas about “big Russian spies” [they do eat a lot of carbohydrates] and our attempts to work out an “arms control for” cyber activities with the Russians.
11. This paragraph gives the gist of the US’s counter cyber policies which basically target Russia, China and Iran. Robert Kanke, NSA director of cyber security policy, summed it up in this quote: “As long as we think we’re getting more value from this set of rules than we’re losing, then this is the set of rules we want to promote.”[So the answer to any question about our counter security polices must be, “Because we think this works better value wise.”]
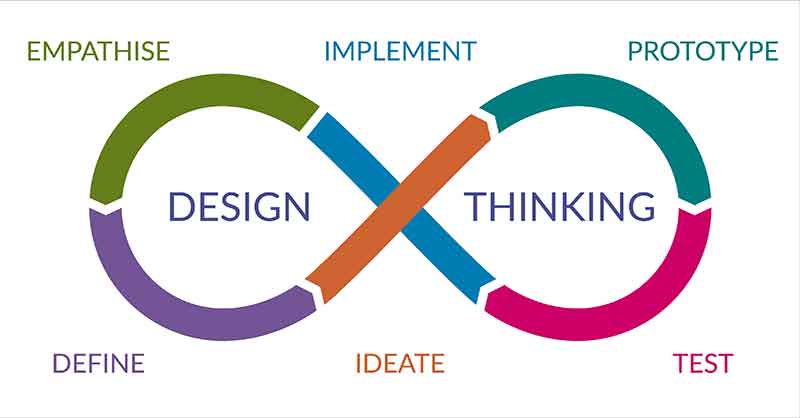
12. A confusing paragraph in which we are told that Russia was developing a “new” doctrine which consisted of “an amalgam that states have used for generations.” This calls for a strategy that says an enemy should be destabilized “at minimum cost” by a combination of tactics: “military, technological, political, and intelligence.” [This seems like common sense rather than some cunning new doctrine.] This has become known as “hybrid war” and because these rather common place observations were written about in an article by the Russian army’s chief of staff (Valery Gerasimov) they have become known as “the Gerasimov doctrine” and although the article was only written four years ago, we are told this generations old amalgam has become “a legend.”
13. We are told Gerasimov is 61, looks stiff in photos and frowns a lot. He thinks future wars will have a four to one ratio of non military (“subversion, espionage, propaganda, and cyberattacks”) to military actions. He writes that the cases of Libya and Syria point out that a basically stable and functioning state can be reduced to “a web of chaos, humanitarian catastrophe, and civil war” in just a few days by a well planned intervention by a hostile state using the tactics listed above. [Although the US has been successful using these tactics in Syria and Libya, it has basically been practicing the Gerasimov Doctrine avant la lettre against Cuba for over 50 years without success so there must be some sort or hamartia within the targeted state for this Doctrine to actually work.)
14. Gerasimov maintains that in the 21st Century the nonmilitary means can often be more effective than the military.
15. By studying primarily the US the Russians concluded that it is very effective to manipulate information technology. Cyber techniques are superior to handing out leaflets or trying to manipulate radio and television.
16. The authors maintain the Russians used these methods in annexing the Crimea and in “pulling off” a “stage managed referendum.” [Other reportage indicates the referendum fairly reflected the views of the vast majority of people living in the Crimea but this article only presents one side of the story].
17. In this paragraph the authors do recognize you can’t use these hybrid war techniques unless there is some basic underlying social contradiction at work. “They are less a way to conjure up something out of nothing than to stir a pot that is already bubbling.” Knowing that they could have been more objective with regard to who put the pot on the fire in the first place. A weakened regional power such as Russia, in a qualitatively inferior economic and military position vís a vís the US since the Soviet Union, a super power, collapsed, is more likely to be trying to turn down the heat to keep the pot from boiling over, a pot others have overheated. If you went to England to stir up dislike of the Queen you wouldn’t get very far as the preconditions for such discontent doesn’t exist. This according to Alexander Sharavin a member of the Academy of Military Sciences in Moscow. But the preconditions to stir up trouble against the political order in the US do pre-exist. [As, perhaps, they also do in Russia].
- Tensions were rising between the US and Russia over the Ukraine and Syria .[it is taken for granted that the US has the sole right to decide the future of both.] The Russians “stung” the US with a “common Moscow tactic” called “weaponized leak” [apparently revealing the truth of an action to the press which the actor would rather not have been known.] What dastardly deed did the Russians do? It seems the US was planning to replace the pro-Russian president of Ukraine with their own puppet behind the backs of the EU and everyone else and the Russians were listening in to a phone conversation between American officials about this plan [the NSA isn’t the only one tapping private phone conversations]. During the conversation it was pointed out the EU wouldn’t like the US forcing its choice for the next leader into office and the response, from Assistant Secretary of State Victoria Nuland, was a very diplomatic “Fuck the EU.” The authors tell us the Russians knew releasing the conversation would cause trouble between the US and EU but did it anyway and, horrors!, no “form of penalty was extracted from Russia” for revealing the truth. [Of course the real issue wasn’t the release of the profanity. It was catching the US plotting the overthrow of the democratically elected government of the Ukraine and putting in a new leader of its choice. That’s what Putin does, not us!]
- It was the kicking out of the elected President of Ukraine that commenced for real the new Cold War but a much more serious kind of Cold War than before.
[The US and EU had plans for Ukraine which included eventual membership in the EU and NATO, the removal of the Russian naval bases in Crimea and the downplaying of Russian influence in Ukraine in general. The Russians responded by asserting their rights and interests and supporting the rights of Russian speaking Ukrainians whose status was being threatened by ultra right Ukrainian nationalists in the replacement government.] How did the US respond to Russia’s not accepting the US plans for the future? Here are the quotes from Benjamin Rhodes, one of Obama’s top advisors who saw the push back as “Russia’s aggressiveness,” according to the authors, and said. “Putin’s unwillingness to abide by any norms [i.e., US norms] began at that point [the forcing out of the elected President]. It went from provocative to disrespectful of any international boundary.”[This respect is not required from American allies such as Israel or from the US itself in its invasions of other countries and bombings across international boundaries. The stench of hypocrisy is overwhelming.]
20. This paragraph reveals two things. First there is a group of hackers called “The Dukes” also known as “Cozy Bear.” Nobody seems to know exactly who Cozy Bear is but “In security circles” it is a belief [but not a known fact] that Cozy Bear is “directed by the Russian government.” Second, the Russian government is building up it cyber defense forces. But, “Very little is known about the size and composition of Russia’s team of state cyberwarriors.” There is then a lot of filler about Russia’s cyber program.
21. Interesting information about how many may be working in Russia’s cyber program. [It seems that many countries are building up their cyber abilities, Russia included.]
22. Cozy Bear [suspected of connections with the Russian government] has tapped into unclassified State Departments computers, unclassified computers in the office of the President and by 2015 “Russian intrusions” into political targets has roused national intelligence director Clapper to tell the Senate the “Russian cyberthreat is more severe than we have previously assessed.” [This is all based on actions by Cozy Bear and neither Clapper nor anyone else seems to know who Cozy Bear really is but the language has shifted from a “belief” to sound like it’s a “fact” that the “Russians” i.e., the government] is doing this spying. This now becomes the main theme in the same mass media that faked the war films from Georgia —that the “belief’ has become a “fact” — it actually hasn’t but it will be drummed into us day and night by the NSA, our politicians, and the mass media that it is a fact, fact, fact, that the Russians are, were and maybe are still inside our internet and websites and our computer systems, etc., that they hacked the DNC and tampered with our elections. Once conjured up this genie of hysteria will be impossible to put back in its bottle or lamp. It will do its job: give us an external enemy upon whom to blame all our woes and to justify even more military spending.]
23. The head of the French spy agency is “reportedly worried’’ that Russian agents are working to help Marine Le Pen. [Well he either is or isn’t worried.] Russian state media [?] have attacked one of Le Pen’s opponents [there are four main people, including Le Pen, running for French president]. A Russian Bank [the authors don’t say it’s a private bank] has loaned Le Pen money. Le Pen also supports the return of the Crimea to Russia. [Russia actually has a fairly good case for taking back the Crimea but the New Yorker article isn’t really interested in presenting the Russian side in an objective manner. This info on France is somehow supposed to make Clapper’s beliefs more like facts but they have nothing to do with Cozy Bear.]
24. Bruno Kahl, the head of German foreign intelligence is concerned “that Russian hackers are also trying” to interfere in German politics. He uses as evidence “Russian interference in the American elections.” [ This is assuming what is to be proved. The belief that Cozy Bear is directed by Russia and hacked the Americans is used as a fact to provide evidence that the Russians want to hack the Germans. The head of German domestic intelligence says hackers are at work in their elections. [Who is behind it all. He doesn’t say].
25. A familiar story. September 2015 FBI warns the DNC that Cozy Bear is cozying up to their computer system. The DNC fails “to mount a full-scale defense.”
26. 2016 a “second group of Russian hackers” [remember it has not been factually established that Cozy Bear is a Russian government operation] called Fancy Bear is messing around in DNC leadership’s emails — esp. those of John Podesta. Both Bears have left their cyber foot prints around the globe. These foot prints are unusual as most change their M.O.s once they are spotted so they are harder to recognize.
27. It is revealed that getting into the email at the DNC and stealing it “didn’t require an enormous amount of expertise”. The “hacking” [it wasn’t really hard core hacking which is entering a system to muck it up not just to swipe info] of the DNC was “mediocre”; it wasn’t done by sophisticated cyber experts. [This would seem to upset the theory that the well trained cyber warriors of the Russian government were behind the DNC email theft. It is perhaps more likely, as some independent experts have suggested, that it was done by a lone wolf (or bear), unaffiliated with any government, who wanted to expose how the supposedly “neutral” DNC was really working for HRC and trying to see that Sanders didn’t get the nomination. But the Democratic Leadership and the Obama Administration has decided to pin it on Putin and on Putin it will remain pinned in popular culture and the mass media; at least for now.]
28. WikiLeaks gets copes of the emails and releases them three days before the Democratic Convention. The fix for Clinton is exposed and the DNC chair, one of the master minds of this anti-democratic authoritarian maneuver [the type of thing Putin is accused of with regard to Russian elections] Debbie Wasserman Schultz is forced to resign. [The FBI is blamed, even though it warned the DNC in advance, by the Democrats for not doing more to prevent the American people from finding out how dishonest the HRC supporters on the DNC were, by investigating and preventing the theft. The revelations soured millions and may have prepared the way for Trump’s surprise victory. You can’t fool all of the people all of the time. Now it’s Trump’s turn.]
29. Donna Brazile becomes interim chair of the DNC but still engages in pro-Clinton activity instead of neutrality. She is fired from her CNN position for giving copies of the questions CNN might be asking at an upcoming debate to the HRC campaign. She doesn’t understand why all the underhanded activity has caused so much resentment against the DNC.
30. A “torrent of fake news’’ about HRC begins to appear on social media. It’s being generated in several different countries (the article implies it’s all from Russia). It seems to be originating from individuals trying to make money from ads on their Facebook and web sites by generating large numbers of “hits” so their revenue will increase. Despite the evidence pointing to this explanation, no one knows exactly who is doing what except for a few culprits who gave interviews to the press, Obama Administration officials who blame all the fake news reports as due to “the Russians” [there is no proof of this] are quoted in the article in a one-sided way. [This in itself is a characteristic of “fake news.”]
31. Some one, or some group, put fake pro-Sanders pages on social media with made up stories about HRC and her campaign. [These were fake news sites created to garner ad revenue due to the many hits they would receive from web surfing] The Sanders campaign said it was being “played” and had nothing to do with the phony sites.
32. More information on the “fake” news phenomena. Automated twitter accounts, known as “bots” and fake news in general ended up producing four times as many pro-Trump as pro-Clinton stories. [This was market driven as Trump generated more hits and ad revenue.] The authors conclude with: “Internet researchers and political operatives believe that a substantial number of these bots were aligned with individuals and organizations supported, and sometimes funded, by the Kremlin.” [Such generalized speculation based on what some people believe is worthless as far as any real knowledge of what happened is concerned. It is just a standard propaganda ploy to plant in reader’s minds that they learned something, when they learned nothing, about the Kremlin. It all boils down to “some people believe the Kremlin did X and some people believe the Kremlin didn’t do X. Readers learned something about some people’s beliefs but learned nothing about what the Kremlin did or didn’t do.]
33. WikiLeaks founder Julian Assange has released 50,000 emails from Podesta’s account and has exposed many underhanded and embarrassing activities of the US government. He once hosted a show on Russian TV. [Fat chance that he will get a show on American TV.] He said about HRC she “will push the United States into endless, stupid wars which spread terrorism.”[ Bush, Obama, and HRC as Secretary of State seem to have already done that. And Trump is on his way.]
34. As more and more HRC campaign emails were released by WikiLeaks, the “Clinton campaign tried to shift focus from the details in the e-mails to the fact that they had been hacked.” [Again, they were not “hacked” in the hard sense; they were not properly secured and were swiped and revealed.] That ploy failed, as people were more interested in what the emails revealed about HRC and her people than in how the information fell into the hands of WikiLeaks.
35. Roger Stone, an erstwhile supporter of Trump, is suspected by some Clinton aides of advising WikiLeaks on the timing of the disclosures. [More speculation, the entire article is basically one big speculation and one wonders what was the point in writing it.] Stone denies it and also denies he has had anything to do with any Russians contrary to any news reports. The FBI never contacted him and he said “If they have evidence of a crime, indict somebody.” [No one will be indicted as a result of this article. Stone’s statement is reminiscent of Putin’s statement that the US, instead making all these accusations about Russia should put up the proof for the world to see or shut up. The US has done neither.]
36. The authors point out that the HRC campaign was committing a lot of “tactical errors without foreign assistance.” They also note that Trump was getting more support “than the media recognized” especially from the white-working class [HRC was taking them for granted — her undoing]. Podesta thinks the emails did a lot of damage. [Actually it was the information in the emails that did the damage. An honest and honorable campaign would have had nothing to worry about].
37. More opining by Podesta who thinks in the end, re the election result, “it’s hard to say if any one thing made the difference.” [That includes the last minute FBI announcement about new Clinton emails turning up, the WikiLeaks revelations, the unsubstantiated charges of Russian hacking, the tactical errors of the Clinton campaign, the unpopularity of the candidate, and Trump’s surprise appeal in the swing states virtually ignored by HRC. It was HRC’s election to lose.]
This is the end of part four. From reading part four of The New Yorker Article you will not have learned anything at all about whether or not the Russian government or Putin had anything to do with the “hacking” of the DNC or if they interfered with our elections. Maybe we will learn something in part five.
Thomas Riggins is the former associate of Political Affairs and a university philosophy lecturer in New York City.